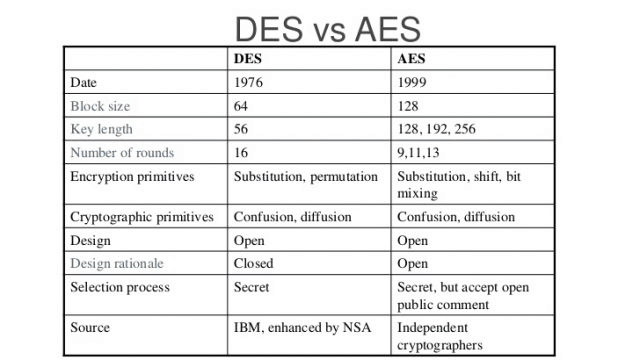
AES Encryption 256 Bit. The encryption standard to rule them… | by Cory Maklin | Towards Data Science

AES Encryption 256 Bit. The encryption standard to rule them… | by Cory Maklin | Towards Data Science

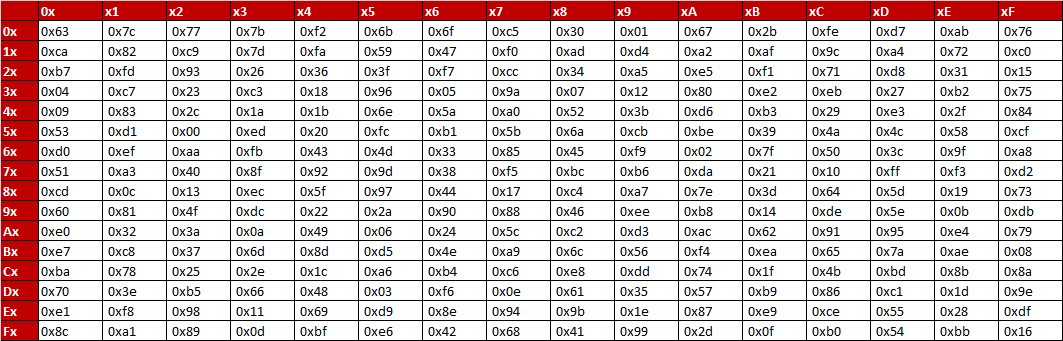
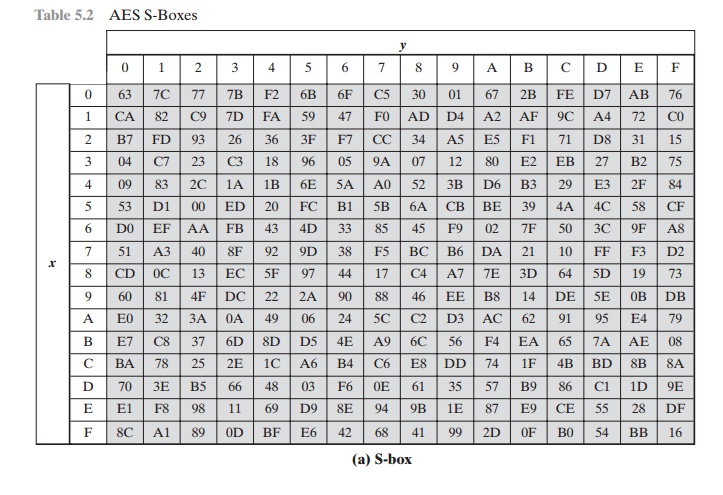
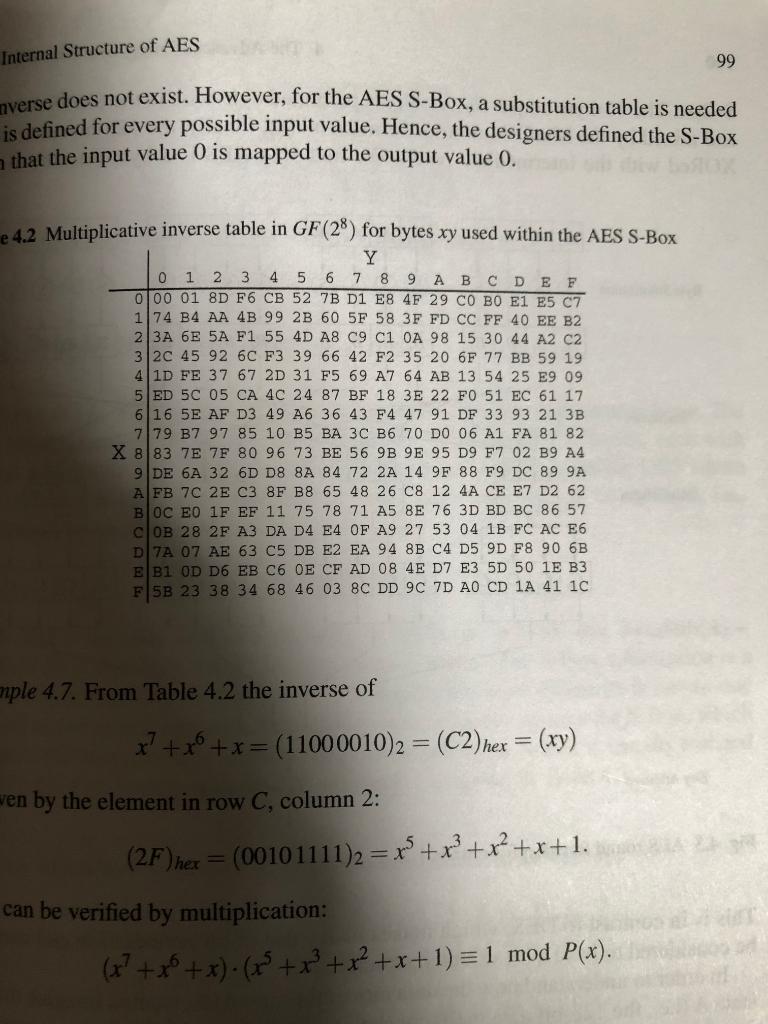
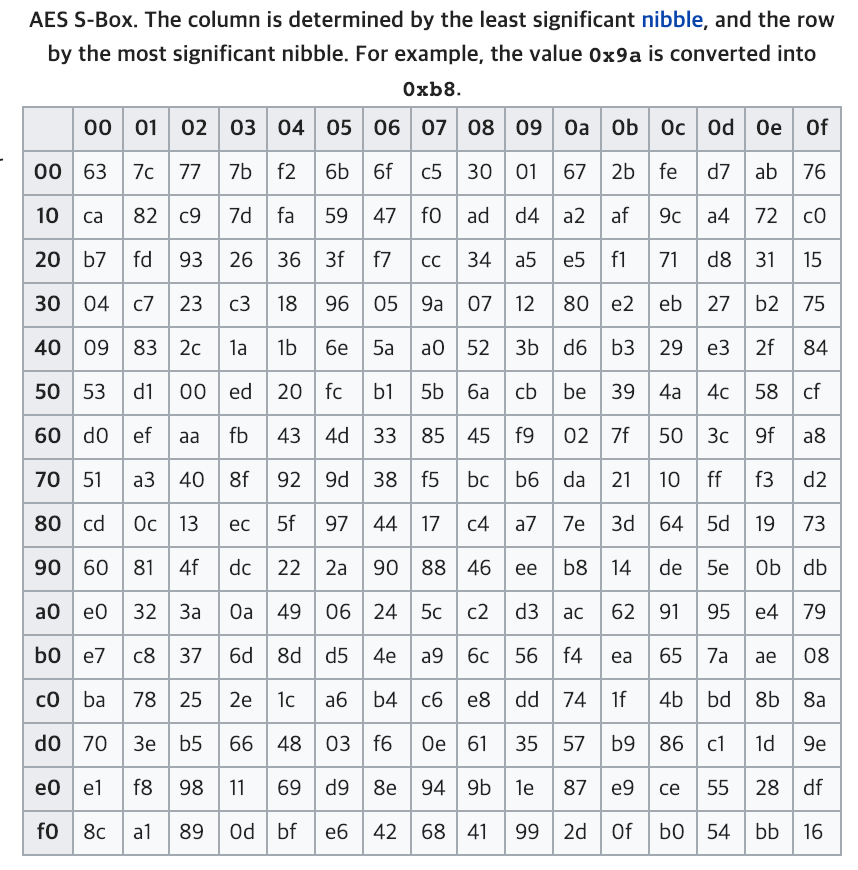
Table 1 from Enhancement of Advanced Encryption Standard (AES) Cryptographic Strength via Generation of Cipher Key-Dependent S-Box | Semantic Scholar
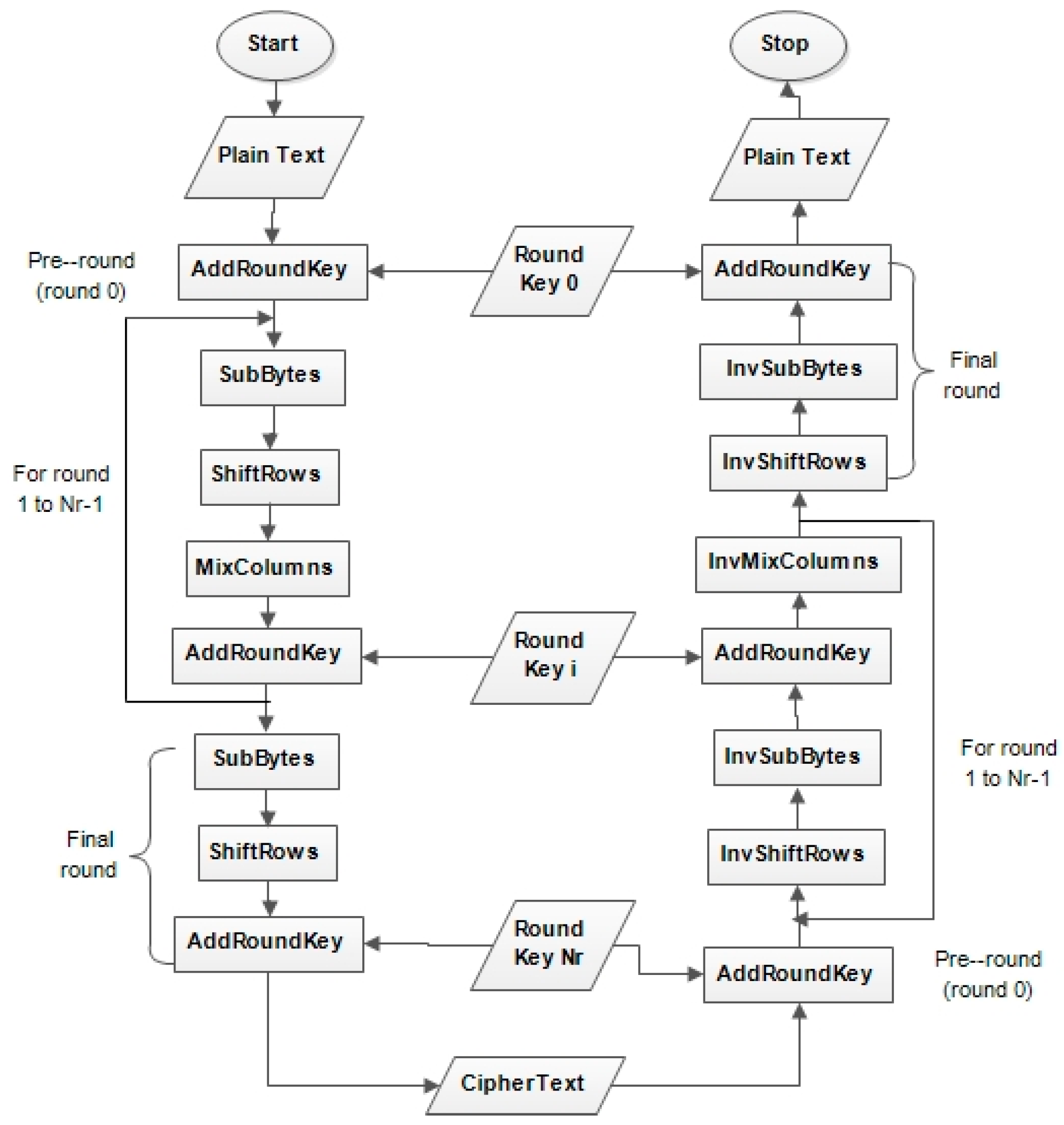
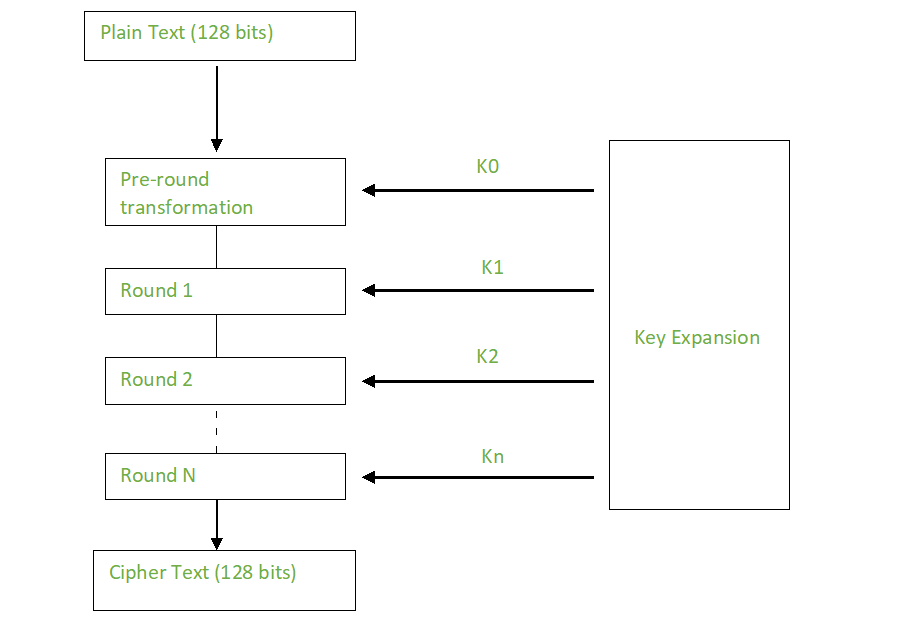
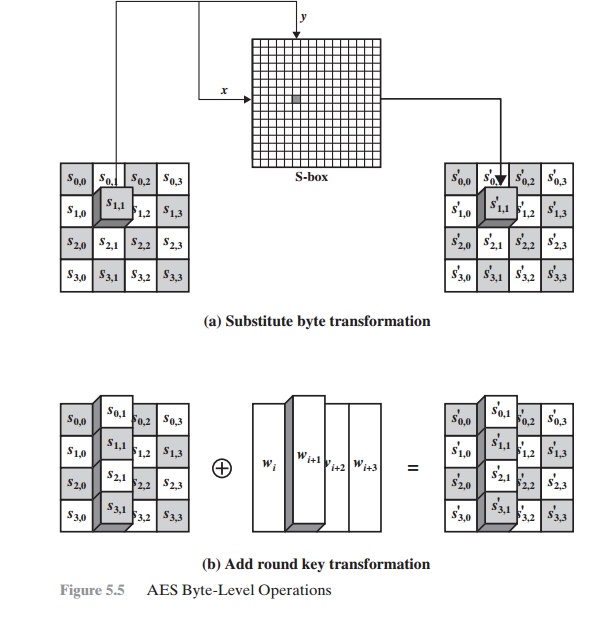
Symmetry | Free Full-Text | Modified Advanced Encryption Standard Algorithm for Information Security